It’s the year 2000, and I’m still working on the virtual mall. The original plan called for lining up deals with distributors, or retailers, or existing online storefronts. I think the idea was that John Business would rent virtual storefronts to people who wanted to sell goods in our mall. I’m guessing those deals have been hard to come by, since it’s been ages since I’ve been given pictures of new stores and products to translate into 3D. At the start of the project I made a couple of demonstration stores, and I haven’t been given any real ones since then.
The lack of new content has given us some breathing room in the timetable. It’s been weeks since Roger – my boss and also a pretty good friend – stopped by my cubicle with a question or request from the people representing John Business, which means I have time to spend on other projects.
Security Through Obscurity

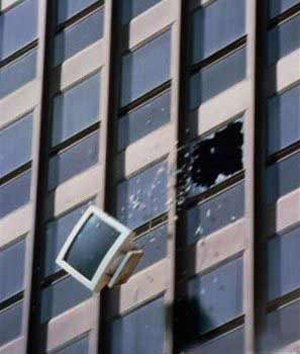
Roger really likes my work and has often wanted to get me the source code for our software. The coders guard the source jealously. Roger – being an executive of the company – technically has access to the source, but only in the sense that he has access to the machine where the source is hosted. He could drive an hour to downtown Boston to our hosting company, go through the layers of biometric securityWhich all seems pretty Star Trek here in 2000. and look directly at the machine in question, but he has no idea where the files are stored, what they look like, or how to access them.
Whenever he asks, the coders always reply with, “Why would you need that?”
Continue reading ⟩⟩ “Crash Dot Com Part 7: The Source”
 T w e n t y S i d e d
T w e n t y S i d e d