For the last several years malicious spam has held steady at around 600 million a day, but in 2009 it jumped up to 3 <carlsagan> billion </carlsagan> a day. (Malicious compared to simply unwanted. The “unwanted” numbers are much higher.) According to the report [pdf file] the increase was due to the increased proliferation and sophistication of botnets.
It’s interesting to note that Adobe Acrobat (and the Adobe product line in general) was by far the leading source of vulnerabilities. Which makes it humorously mysterious as to why the people who put the report together chose to package their findings inside of a pdf file. Okay, the report itself is not a source of infection, but the second biggest problem* with Acrobat is that people routinely use it for packaging information that would be more useful in simple HTML. Let us not further legitimize this practice using a document outlining the dangers of this practice.
Anyway. Botnets. Botnets is such a strange term. It makes it sound like there are these legions of networked robots, like the Geth all nestled into cold metal racks, ticking away the time thinking malevolent computer thoughts about the worthlessness of fleshbags. But the truth is that a botnet is simply a bunch of compromised machines owned by the clueless, the uneducated, the irresponsible, or the idiotic. When your friend asks you to come over and help fix their computer and you find the thing is overrun with mysterious and malicious processes, you’re not just looking at a hosed computer. The machine in front of you is most likely given over to the service of the baleful and dangerous machinery that poisons the network every day. People frequently gesture vaguely in the direction of Russia or China when speaking of mysterious cyber threats. But the real threat is coming from your buddy’s PC because he downloaded and ran a program he shouldn’t. The emails may have been authored in far-off lands (maybe) but they are being sent from his computer and millions of others like it.
My wife seems to be the go-to woman around here when computers go bad among friends and family. (People used to call me all the time for help with these sorts of problems, since I’m the “computer guy” to them. But every. single. person. owns a dog or a cat, and I’m very allergic. Which means I can safely and honestly refuse for health reasons instead of needing to invent some other excuse.) My wife is cursed with a rare form of perseverance and generosity that compels her to take on these sorts of jobs. She used to simply install AVG anti-virus and have it cleanse the machine, but over the years the threats have grown more sophisticated. She eventually encountered a machine that wouldn’t let her install SpyBot or whatever other tools she needed. The malware was purposefully defending itself. This, along with the risk of missing unidentified threats, caused her to adopt a scorched-earth policy: If you call Heather she will fix your computer. But she will do so by installing the operating system fresh. Oh? You’re disappointed that you lost all your settings and that cute little screensaver of the bunny you loved so much and now the machine has forgotten all your passwords and bookmarks? Well maybe next time you should think twice before downloading software from www.microsoft.f3gxq9i12p.com/totallylegit/trustus.html.
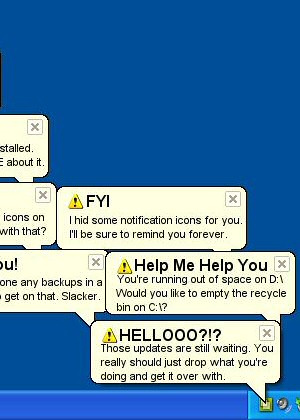
I kid. Sort of. It’s easy to get frustrated with people who fall into these traps, but the truth is that a lot of the knowledge we take for granted took years to acquire. How to spot a bogus URL. Or understand the difference between a link and the text that encapsulates it. Or spot a phishing email based on the lack of proper https. Or how to identify dangerous or potentially dangerous documents. (pdf files.) Or when a site or email is asking for information they should already have. Or how to tell that this popup window didn’t ACTUALLY scan your computer and find a bunch of viruses.
The truth is that you could spend many, many hours educating someone so that they don’t fall for these scams that seem to be so insultingly transparent to others. The problem is daunting. Most people don’t want to have to become computer literate in order to use the net. You don’t need to be “TV literate” or “phone literate” or “DVD player literate”. The knowledge you need to use these devices is small and the dangers of ignorance are small or nonexistent. But you can get yourself into a great deal of trouble with the internet, and if you screw up your problems become everyone else’s problem. What we’re seeing is a more perilous version of the “blinking 12:00” problem that we saw on all VCRs in the 80’s. The tech requires more education than 95% of the people are willing to acquire. (This isn’t just an age thing, either. There are plenty of young people who make these mistakes.) They see the PC as a piece of entertainment equipment (and for them, it largely is) and they just want to push the buttons and have it work. Historically, this isn’t an unreasonable thing to expect. Only now instead of having the VCR blink 12:00am to announce their lack of technical knowledge, their computer is conscripted into the service of people who are undeniably evil and destructive. It would be one thing if their computer just stole their credit cards and that was the end of it. But instead the machine begins sending out emails, posting comments to websites, co-opting the user’s Twitter and Facebook in order to ensnare their friends, and generally making a great deal of trouble for everyone else.
It’s a technical problem, but it seems to need a social solution.
* The biggest problem with Acrobat is the security vulnerabilities. The third is that it’s just plain awful software.
 Shamus Young is a programmer, an author, and nearly a composer. He works on this site full time. If you'd like to support him, you can do so via Patreon or PayPal.
Shamus Young is a programmer, an author, and nearly a composer. He works on this site full time. If you'd like to support him, you can do so via Patreon or PayPal.
 T w e n t y S i d e d
T w e n t y S i d e d