Heads up: This post is a bit more dashed-off than my usual columns. I actually think this would eventually make a good video for This Dumb Industry, but I need to do a ton of research before I can commit my thoughts to the indelible format of a YouTube video. For right now, this is mostly me thinking out loud.
Anyway…
So the news is that someone hacked into CDPR’s server, downloaded the source code for several games, then locked the files and held them for ransom. When CDPR refused to pay, the hackers “sold it on the Darkweb for 7 million“. The hackers obtained the source for Witcher 3, Gwent, and Cyberpunk 2077. From here on I’m going to talk about the Witcher 3 source, but most of this is applicable to all of the games.
My question is this:
What in the world are the buyers planning to do with the source?
This Makes no Sense
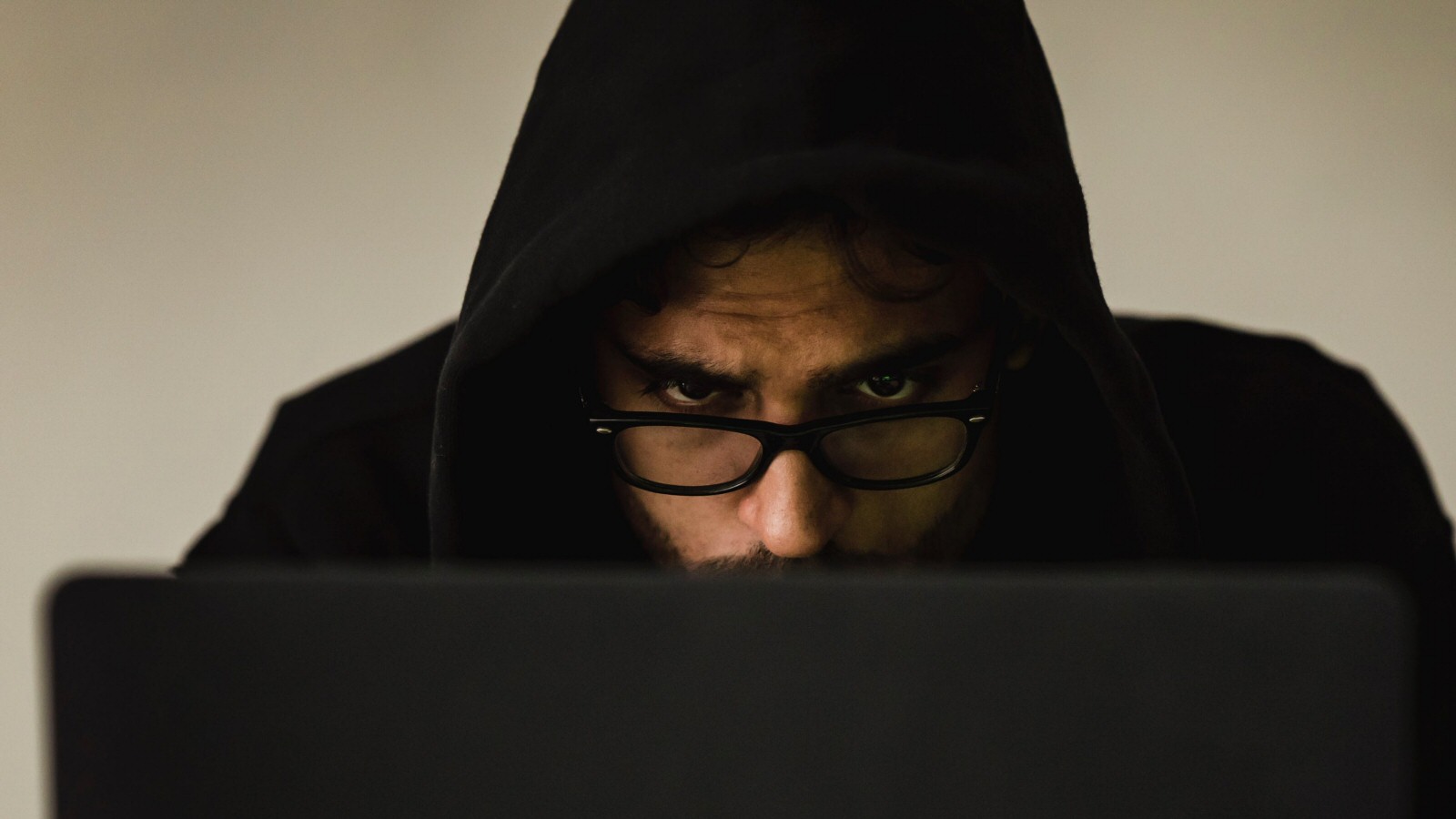
Yes, it’s cool to have the Witcher 3 source, but 7 million is a LOT of money for something you fundamentally can’t use.
Now, maybe you want to assume that the buyer is so fabulously rich that they’re willing to drop millions of dollars on something that can never yield a return and he’s just planning on printing out the source and putting in a little lightbox to look at once in a while. Like a lunatic. If that’s what you think happened, then fine. You don’t need to read the rest of this. We can all shrug our shoulders and marvel at the deeds of people with more money than brains.
But let’s assume, for the sake of argument, that this buyer is a hopeful young criminal, looking to make some money with this. If that’s the case, then he’s probably looking to launch his own game studio. He bought this code, hoping to bootstrap his studio by buying the stolen source code rather than spending years developing his own game engine.
Let’s call this outfit Top Sneaky Studios. The CEO is Brandon Sneakman. To give him a break, let’s assume he’s going to use this appropriated engine to make (say) The Witchman ChroniclesClearly this name is way too obvious. I chose the name because it’ll hopefully be easier for you to remember. Hopefully Brandon has the sense to come up with more original branding.. That’s smarter than trying to make a space adventure or an open-world modern city game from an engine designed for medieval fantasy. I’ve worked on both cities and pastoral landscapes. Trust me, they’re VERY different! It’s no good paying millions for an engine if you’re going to have to re-write the dang thing.
But even if he just wants to just make a Witcher clone, Brandon is still doomed. How doomed? Listen…
1. You would get caught like, right away.
Keep in mind that it’s incredibly common for AAA games to attract a modding community. People regularly datamine games to see how they work and how they were made.
(Now maybe you want to argue that Top Sneaky Studios aren’t AIMING for AAA. Fine, but paying 7 million for an engine is a very non-indie move. Most indies don’t MAKE $7 million, so you’re in the hole before you even begin work.)
In any case, while doing this datamining people will notice things:
“Oh hey, check out these data structures. There is a limitless variety of ways to represent game concepts in memory. I’m talking about things like an NPC, a weapon, a quest, etc. And yet this game JUST HAPPENS to have the exact same memory layout as Witcher 3. The odds of that being an accident are approximately 1 in impossible.”
“Check it out! This game runs its rendering pipeline in a background thread, then it has three general workhorse threads for streaming in content as the player moves around the world. Then a physics thread, a thread for pre-streaming cutscene dialog, and another thread for playing audio. That’s the exact same setup they used in Witcher 3Not really, I’m just making up an example.. The odds of two different engines randomly having the exact same thread structure is miraculous.”
Remember, the public knows that the code for Witcher 3 was stolen. A lot of curious people are going to be looking for it now.
Sure, if the folks at Top Sneaky Studios know what they’re doing then they would be able to change this stuff to cover their tracks. Still, there’s a ton of ways to get caught. There are a lot of different ways to uniquely identify data structures, program flow, savegame data, game asset storage, thread behavior, and the overall structure of game objects. And I’m willing to bet that the ways I know about are vastly outnumbered by the ways I don’t know about. Better hope you don’t miss anything, because getting caught opens your entire enterprise up to both civil and criminal charges.
2. The two games would have the same dependencies.
We don’t need to engage in super-technical data mining to see what’s up. If you’ve got the game installed, then all you need to do is open up WitchermanChronicles/bin/x64/ and look at the list of external DLLs. If you look in that directory you’ll see stuff like PhysXPhysics engine SDK., NVHairNvidia’s hair simulation SDK., APEX_ClothingI’ve never heard of this one, but obviously it’s a fabric solution for flowing capes and such.. In fact, there are a total of 24 DLLs in your Witcher 3 install. If Top Sneaky doesn’t want to have the smoking gun of the same DLLs, then they need to either license something different or write their own. Either way, that’s a bunch of programming that needs to be done.
I’m not sure how it works today, but back in the 90s you needed some sort of developer key to compile a library. I’m hazy on the detailsI THINK I remember your key was a simple file you kept with your source code, and inside of the text file was some huge 20-digits number., but you basically had to “sign” your particular install. From here you have four options:
- Use the CDPR license keyThe key was certainly stored with the stolen code, so Brandon ought to have it., and thus announce to the world that this game is built on top of the stolen source.
- Use a nonsense keyThis probably involves some DRM-removal, but I dunno. I’ve never tried it., thus making it really obvious that you don’t have the proper license for this particular SDK.
- Roll your own replacement. This means giving your engineers time to familiarize themselves with this “new” engine. In a normal company, you’ve got old-timers to help guide the new coders through the code and answer “How do I do X?” type questions. But if you’re using a pilfered engine then everyone on the team needs to grope around blindly. Nobody knows how it works, and you can’t ask Google for answers because this sort of knowledge isn’t available to the public. I’m not saying it’s impossible, I’m just saying it’s really time-consuming.
- You could obtain a fresh license for this stuff. However, that seems sort of unlikely to me. The sort of person who would purchase a bootleg game engine on the DARK WEBSeriously, the news media LOVES stories about the dark web. They don’t understand it, but it sounds exciting and illicit and it’s easy to get people to click on links about the DARK WEB. is probably not the kind of person that will scrupulously adhere to licensing rules.
However it works these days, I doubt this system has become LESS restrictive since the 1990s.
And once you fix this problem, you still have the issue that Witcherman Chronicles is going to have the exact same / very similar profile of external DLLs.

3. A game engine isn’t just the “game”, it’s also the internal tools.
So Brandon has a problem. He wants to hire a team of artists to make his game. However, he can’t just create a job listing that says, “Preferred: 2+ years experience with the CR Projekt RED toolset”It’s actually called the RED Engine.. That would be a dead giveaway.
So he needs to find workers, but he can’t openly ask for the skills he needs. Worse, CRPR has shown off their tools in public videos like this one. Sooner or later he’s going to hire someone that sits down to work on the first day and thinks, “Holy shit. This looks EXACTLY like the thing CDPR uses to make their cutscenes and dialog sequences!”
If Brandon is the kind of person to buy stolen source code, then he’s very interested in taking risky shortcuts. This means he’s probably not the kind of leader that’s going to spend a lot of time worrying about morale and the well-being of his staff. Top Sneaky Studios is probably destined to be a place with forced crunch and low pay, thus increasing the proportion of disgruntled workers.
What are the odds that someone on the team will call the authorities, or send an email to Jason Schrier, or just post the truth somewhere on Reddit? Actually, that’s the wrong way of looking at this. Instead we should ask: What are the odds that everyone keeps the secret FOREVER? This is quickly turning into a conspiracy that requires perfect loyalty from a large group of people who do not personally benefit from the secret, but would benefit if they divulged it.
4. The Witcher 3 engine is friggin’ OLD.
If Brandon manages to get his studio off the ground this year, then he probably can’t hope to ship Witchman Chronicles before 2025. Witcher 3 came out in 2015.
Is Brandan planning to spend additional time and money doing a drastic overhaul to the rendering code, or is he planning to release a game in 2025 with graphics that are a decade out-of-date?
(Yes, the code for Cyberpunk is much newer, but it’s also incomplete and janky as hell. The programmers at CDPR might be able to patch the game up in half a year or so because they’re familiar with the code, but if you’re starting with a new team then that same work is going to take much, much longer.)
5. The Unreal Engine is WAY Cheaper!
You want to make a AAA game? You can use the latest, greatest Unreal Engine FOR FREE up front. You don’t need to pay anything until your game makes $1 million. After that, you just pay Epic 5% of any further sales.
The crossover point here is $141 million. By that point, you’ll have paid $7 million to Epic. Above that point, and using the stolen engine is cheaper. Below that point, and Unreal is cheaper.
So you can:
- Use the cutting-edge modern engine that costs nothing up front and only costs money if you make money. There are tons of people familiar with this engine and finding them is easy.
OR…
- Pay 7 million up front for access to an outdated engine that needs millions of additional dollars to bring it up to date and conceal its origins. People familiar with the engine aren’t as plentiful, and you can’t look for them directly. This option carries the added risk that if you miss something, then your crime will be exposed and your entire company could be ruined. Additionally, you need to maintain an iron-clad conspiracy. This entire plan makes no sense.
So What’s Going on Here?

It’s conjecture time:
- The hackers didn’t actually sell the engine to anyone. This was all done with sock puppets so they could claim they pulled off a $7 million heist. Because that sounds better than admitting in public that nobody wanted their stolen goods.
- The hackers didn’t actually steal the source in the first place. Maybe they messed up at some point. They locked the files, but they didn’t successfully download the entire dataset before someone discovered the breach and locked them out. Think about it. They “sold” the engine to a buyer under the condition that the buyer would never release the source. This allows them to claim they stole the data without ever furnishing proof.
- Everyone in this story – CDPR, the hackers, and the buyers – is an idiot.
I don’t know what the truth is, but I’m extremely reluctant to take the black-hat hackers at their word.
Footnotes:
[1] Clearly this name is way too obvious. I chose the name because it’ll hopefully be easier for you to remember. Hopefully Brandon has the sense to come up with more original branding.
[2] Not really, I’m just making up an example.
[3] Physics engine SDK.
[4] Nvidia’s hair simulation SDK.
[5] I’ve never heard of this one, but obviously it’s a fabric solution for flowing capes and such.
[6] I THINK I remember your key was a simple file you kept with your source code, and inside of the text file was some huge 20-digits number.
[7] The key was certainly stored with the stolen code, so Brandon ought to have it.
[8] This probably involves some DRM-removal, but I dunno. I’ve never tried it.
[9] Seriously, the news media LOVES stories about the dark web. They don’t understand it, but it sounds exciting and illicit and it’s easy to get people to click on links about the DARK WEB.
[10] It’s actually called the RED Engine.
Playstation 3
What was the problem with the Playstation 3 hardware and why did Sony build it that way?
Games and the Fear of Death

Why killing you might be the least scary thing a game can do.
Spec Ops: The Line
A videogame that judges its audience, criticizes its genre, and hates its premise. How did this thing get made?
Seven Springs

The true story of three strange days in 1989, when the last months of my adolescence ran out and the first few sparks of adulthood appeared.
Raytracing

Raytracing is coming. Slowly. Eventually. What is it and what will it mean for game development?
 T w e n t y S i d e d
T w e n t y S i d e d

That quote is giving me “my Uncle works at Nintendo” vibes.
I’ve got no idea how you lock a file (and I have trouble getting my head around any programming concept more complicated than basic arrays), but what does that actually achieve for the hackers in the long run? Couldn’t CDPR just hire a white hat to unlock them, for way cheaper than the black hats are demanding?
Depends on the “locking” mechanism. I’m assuming it’s supposed to be that the code was encrypted on the server using a key only known to the hackers, and the original files deleted (this is a pretty classic ransomware approach; give us money and we’ll give you the key that lets you get your data back).
Assuming CDPR has any kind of competent backup system they would probably just restore from backup and take the hit of any data loss that incurs (anything that had changed since the last backup was taken), which might be why they didn’t pay out (in fact, I have just read the article and it says this very thing).
According to news reports CDPR indeed just pulled out their backups, tightened data security, and ignoredthe demands.
Well, unless CDPR are even more idiotic than recent events suggest, all their stuff is backed up daily, or hourly, to multiple independent, offsite and system isolated backup locations, both virtually and physically. So, no, they probably didn’t actually get to lock anything more important than today’s work, realistically. Or, that day’s work. But what I assume Shamus means is they encrypted the files, ransomware style.
In any case most of the article is countered by the supposition that Brandon lives and works in China. Where they don’t have to Care about getting caught. Look at Genshin Impact, for chrissake.
That’s a good point, and China does indulge in this kind of espionage. But is CD Projekt’s source code really that valuable now? We’re a whole generation on from the Witcher 3 and Cyberpunk isn’t exactly the role model for stability.
Even with the crazy games budgets of AAA development $7 million is a hefty chunk. You’re going to need to find a lot of gold in that source code, above and beyond what you’ll get from the Unreal engine.
Perhaps it makes sense if they lied about the price.
Ehh, other comments seem to be suggesting that 7 million figure is largely just smoke and mirrors, so who really knows. But tbh I brought up Genshin as an example of how Witcher 3 code and art might still be quite valuable – if the plan is to bring out a mobile game, that maybe can also be on more traditional platforms as well.
Why pay 7 million dollars for a bunch of art assets when you can just steal those same assets from the end product for free, and then pay a couple of your artists to touch them up, to make them suitable for your own crappy mobile game?
I wasn’t aware Genshin Impact has been accused of code theft! I mean, I know it’s copying its some of its traversal mechanisms and aesthetics from BotW, absolutely, but that’s legally super ok. Actual code copying is a whole different bucket of fish.
Do you have any links about this?
China isn’t some parallel universe where none of the rules of logic or economics apply.
1. Why pay 7 million dollars for the source code to an esoteric engine that you will get zero technical support for, and have zero people that you could hire that have any experience with it?
2. Even assuming CDPR is completely incapable of suing you in China (Which was a safe assumption to make in 2001, but is by no means not a safe assumption to make in 2021), why would you completely burn any ability to sell your product on an international market?
3. Suppose that like everyone else in the gaming industry, you are backed by a publisher. CDPR will now seek an injunction against international sales by that publisher in any market they can.
I think it means that the files were encrypted with ransomware, making them unreadable unless you have the right key. The hackers demanded money from CDPR for the key (effectively, holding their files ransom) and apparently also threatened to sell the unencrypted files to a third party if they don’t pay.
If the ransomware does the crypto right, then it’s practically impossible to unlock the files. That tends to be a big “if” with ransomware, though. Also, CDPR probably has a backup on a machine that the ransomware didn’t get to, so it doesn’t really matter anyway.
Every code base I’ve worked on since around 2010 has used a form of distributed source control. With mercurial, every clone is a complete copy of the entire repo and all its history. Git doesn’t do that automatically for every working copy, but I like to grab a bare close to work from.
Ransomware doesn’t work when the target has any backups. In most modern dev shops, *every developer* has a complete copy of the code base. Trying to run a ransomware scam on a software company is monumentally stupid.
I doubt they lost any work at all, other than the opportunity cost of fixing their servers.
CDPR didn’t have to unlock anything. They had backups because, although the state of Cyberpunk 2077 suggests that they are bad at project management, it seems they are not completely stupid. The hackers have inconvenienced and embarrassed CDPR, but they haven’t actually hurt them.
Trashing a week’s worth of work and having to fart around with the backups still costs real money. Having done Project Management work, that definitely hurts.
Remember that most (if not all) of their developers have a full copy of the latest-and-greatest on their own personal machines.
So their IT dept has to spin up a clean machine from their backup, then the devs have to do a relatively simple diff and check-in their local copies with the work they’ve done since the backup.
So in reality, they lose a day, perhaps two of development time – which is still a lot of person-hours – most of which is due to everyone needing to update their certificates and trust chain etc after all the “possibly dodgy” certificates have been revoked.
Loads of work for IT, some work for the rest but not ruinous.
When they say “locked”, they mean encrypted with a sufficiently strong key such that a victim cannot reasonably, reliably decrypt their data unless they pay the ransom to purchase the key to decrypt their (now completely unusable) data.
Of course, this entire scheme is pretty much instantly defeated by a component DR plan with a good set of off-site backups. It’s pretty shocking how many people can get stung by ransomware, though, and not have a way out.
That’s why a lot of these schemes target governments, especially smaller entities like cities or individual departments. They’re usually cash-strapped, under-staffed, report to public stakeholders with a poor understanding of cybersecurity issues, and are often dealing with privacy regulations prohibiting the offshoring of data concerning citizens and taxpayers.
Just gonna give a blanket thank you to everybody who explained how ransom ware works, that makes a lot of sense.
… and I need to start backing up my files
My uneducated guess is that some other big-name AAA studio might have bought the code for reverse-engineering purposes (there’s probably a lot of systems in that source that even if you cant just copy-paste you could save a lot of time just by having a working example to start from). Whats the phrase, corporate espionage?
That would make sense, though the the price-point would have to be more modest. You could probably get a few bites on ‘$700 to see what the competition is doing’.
I just don’t think the other big studios are this dumb (and I credit them for a whole lotta dumb).
First of all, game engines aren’t the same. A really elegant trick in one engine won’t necessarily mean anything in another. The W3 engine isn’t so mind blowing that it can do things nobody else can approach today. Sure, Cyberpunk has done cool stuff with everyone being a named character. How you’d port that into a competing engine is less clear.
Which brings me to the related point. Dev teams are large. What you’re doing is clearly illegal. You would have to do this in secret with a small cadre of trusted engineers. Which, maybe, fine for the analysis. But then you ALSO need to modify your game engine to use the stolen techniques. And that’s not how you do your other engine changes. You’re not getting 5 secs around a whiteboard hashing out how to approach a problem. You’re going to have some people who already know the answer off writing significant amounts of code on their own. It’s going to be very, very hard to conceal from your dev team that something’s not right here. Even the ones not directly seeing the stolen code.
And then all you need is one developer who feels aggrieved. Too much crunch? Let go unceremoniously after shipping a successful game? Didn’t get the raise they wanted? Consider how much leverage you’ve given even the “trusted” group.
Knowingly trafficking in stolen goods is “go to jail” crime. Not “pay a fine no admission of wrongdoing” crime.
The “big studios” are also not going to be able to spend 7 million without people noticing.
It doesn’t matter how big the company is in aggregate, as you go down the ladder you have people keeping track of smaller and smaller amounts of money. Somewhere in the company, someone tracks the expenses of the office coffee machines as part of their job. $7 million can’t just disappear from the books.
Nonsense! Happens in the movies all the time, there is always a slush fund for black-ops… :-)
I agree with you.
Even if I’m Evil McSleazebag, Project Manager Without Remorse, I can still do the math of what exactly I’m buying. If I need my “trusted cadre of engineers” to reverse-engineer this and have the discretionary spending I can write off to buy code from code-thieves, I could also just legally and legitimately spend that money on paying my own engineers to develop stuff in-house.
Accounting won’t be asking as many questions about where the hell that money went. I’m not exposing the company (and my own posterior) to legal consequences. Maybe my team would even enjoy it – not that I really care, beyond the exploitable value of temporary morale boosts.
There may be a price-point where buying this illicit code could make sense; that I expect to get so much reverse-engineering value that it’s worth the risks, the trouble of consorting with thieves, and so on… but I doubt it.
Seriously though. If I wanted code improvements to my own in-house shit and had $7,000,000 or more to spend, I’d probably just charge a bunch of coder-hours to overhead and fix my own shit. Then I own everything and I have no risk.
That’s a really good point: If you pay $7 Mio, how want to get profit on your investment.
Reverse Engineering as in the last comment is indeed the most likely reason, though for 7 Mio you can get a lot of development effort on your own. So it’s probably not reverse engineering for training or have a look at maybe intresting concepts.
If someone actually put down the money for the source code as the hackers suggest (and I’m with Shamus here that this doesn’t mean someone actually did), their hope may be to reverse engineer the code for weaknesses and use them either as attack vectors (buffer overflow by loading a data file anyone? Doesn’t matter if its a word doc, a manipulated image file or a savegame file) or as cheats.
These are basically the two things that could be derived from (stolen) code and resold for money.
Ooh, trying to pwn any machine running W3, now that’s nefarious.
Yup. CDPR’s games have an online component, so there must inevitably be vulnerabilities in the code. I’ve been wondering whether to uninstall Cyberpunk for that reason.
OTOH given how it was developed, Cyberpunk’s code base is probably such a mess that nobody can find any vulnerabilities among all the bits of non-functional code that got disabled at the last minute, when they finally gave up and shipped it.
You forgot a possibility: China. IP theft is rampant, the market is huge, and if a future game is released in Chinese for that market, odds are the mod community won’t notice. Even if a blatantly obvious clone of The Witcher 3 is released globally, and people in the West notice immediately… It’s China, what is anyone going to do about it?
This was my immediate thought upon reading the article’s opening.
You’re missing a possible motive: the hackers bought CDPR’s code for the same reason the Rebels stole the Death Star plans. They didn’t want to build their own Death Star, they wanted to find the weak spot and blow it up. I don’t know if Witcher 3 has any online components, but Gwent certainly does and if there’s some obscure vulnerability buried in line #285395 of the Gwent source code then you might be able to upload a virus to the computer of everyone who plays Gwent. From there you could do anything, the most obvious path to profit being to steal the credit card information users enter to buy microtransactions.
I have some serious doubts that any hackers would pay $7 million for that. I don’t actually know how much the going price for working zero-day exploits in the dark web is, but I strongly suspect it’s not going to be seven figures, even if you pay for exclusivity. Add in the fact that it’s going to be a lot of work to find those exploits(and you don’t really need the access to source code to find them; see any windows vulnerability for an example) and that you have no idea how many/how severe exploits you’re going to find, and that sounds like a terrible deal.
I’m honestly not savvy enough to figure out what this could be used for. Is it possible to find exploits that can be used maliciously and would not be easily fixable (like with the modded content)? Does it offer any insights for existing AAA competition that would be worth 7mil (and the risk no matter how negligible)? From a layman’s perspective I have to agree that I can’t think of something that would realistically be worth it and this sounds like smoke and mirrors meant to increase the hacker’s rep and/or scare any possible victims of similar attacks (“if CDPR’s code was worth 7mil we should pay the 1mil before ours is sold”). Now I’d just wait for the rumour mill to start spewing out something like “my Steam account got hacked with stolen Cyberpunk code”.
Edit: I see people speculating along the same lines above. Writing a comment from work is sloooow…
Well, people have already made the same speculations I made before I got the chance to comment, so there’s not much else I can say. I guess there’s always the cynic possibility that CDPR just made the whole thing up to distract people from Cyberpunk 2077’s issues or to try to gather some much needed sympathy towards them. At this point I wouldn’t put it past them, sadly.
Yeah, it would be almost impossible to detect if CDPR “stole” the source from themselves, especially if they were at all clever about it. Motive? It gives CDPR an excuse to re-write their core technology from the ground up instead of patching CP-2077 incrementally.
I think this question is a good one. Shamus spends most of the post debunking one possibility (develop and release a AAA game using the stolen source as a base). So that’s either not the plan or a bad plan.
Others in the comments to date have suggested some possibilities:
• Release a AAA game in a country with lax IP laws where they won’t care it’s stolen (e.g. China)
• Analyze the code looking for weaknesses, so they can use the existing Witcher/Cyberpunk installs as a Trojan to deliver malware.
Some others come to my mind, of varying degrees of plausibility:
• Examine for arguable violation of software patents, then tip off the appropriate patent trolls for a percentage of the take.
• Look for the next “hot coffee!” scandal on cut or later modified content, use for stock price manipulation (short CDPR/its distributors, break the news, make money on the stock price hit).
• Chop shop it – break off specific parts of the engine and development tools, give them a light polish code changes, then license “your” tools to small and upcoming game studios. You don’t have to use everything – just take the parts that seem generally useful and sell those off.
Other ideas?
Some really, really, disgruntled CP77 buyers out for revenge and making up the part about selling it?
There’s also the… financial liberties of underground markets – it’s probably unlaundered money being used.
And I suppose you’d get the backdoor into CDPR’s intranet as an added benefit. CDPR clearly did not manage to close that hole last time they were hacked (1-2 years ago IIRC).
Disgruntled employee perhaps? That’s usually how competent high tech companies get broken into.
All I see here and in the original message (I might well have missed something, as I just skimmed the original) is $7 million. I don’t see anything that says 7,000,000 USD. Perhaps they sold the source for 7 million Zimbabwean dollars (a bit over 19000 USD when I looked and probably quite a bit less by the time you read this).
Or, as Shamus suggested, maybe they’re lying. (I think that latter is very unlikely though; who wouldn’t trust the unverified claims of extortionists?)
Maybe, but usually when people just say “$X dollars” they mean American dollars
Perhaps it’s 7 million eddies?
The company that commits crime and also mistreats their employees cracks me up. Worked for at least one of those before.
Yeah, I don’t think anyone gets much value out of a dump of source code, however valuable the product, unless it’s really niche.
My best guess is that it didn’t really happen.
My second guess would be, you don’t try to use it to develop anything, you just publish “cyberpunk 2077” in countries which don’t enforce copyright much. That only makes sense if that’s easier than buying a copy of the game and cloning that.
My third guess would be, someone was really stupid and didn’t understand what they were buying, or paid in cryptocurrency that is notionally worth 7m but couldn’t actually be cashed in.
“Looking for exploits” is a good explanation for source code value but doesn’t really make sense for a computer game.
That’s not a thing. How do you think “worth” is determined? The only source of that is the going rate for that currency on the exchanges. If you have seven thousand ThiefCoins and they’re trading for $1000 each, you have $7 million worth of ThiefCoins and you can cash that in by showing up to the exchange and saying “sell please”. This pretty much only stops working if you are Satoshi Nakamoto and own such a large share of the currency that trying to sell it all would result in an overall shift in the market.
That said, they didn’t actually get $7 million, see my comment below.
They actually didn’t. The $7 million figure comes from the auction being posted with a $1 million opening bid and a $7 million buy-it-now price. The thieves later closed the auction saying “an offer was received outside the forum that satisfied us” with no information available on how much it was.
Also, bear in mind that there’s no evidence this was ever real. Some anonymous dude showed up on a forum saying “I have CD Projekt’s code, anyone wanna buy it from me?”, other posters mostly scoffed at the idea, then our guy says “Welp, I sold it to someone, bye.” Nevermind the idea that he didn’t really make the sale, we have no evidence this guy ever even had the code, he might have just been some liar.
I think even the most likely explanation “evaluating the code for malware exploits” seems pretty unlikely for the price tag. Who’s going to pay SEVEN MILLION DOLLARS for the CHANCE that MAYBE you can find an exploit on machines that still have the Witcher 3/CP/Gwent installed?
I don’t know much about hacking or whatever, but that’s a HUGE gamble with not much upside at all. Even if you do manage to get an exploit, it’s probably not going to be 100% effective, and then it only applies to machines that still have one of the apps installed. So your pool of potential victims is already capped fairly low (by comparison to targeting, say, a windows exploit). On top of that, you’re really only infecting gaming PCs, and you’re unlikely to get any company assets, which is where the big numbers and big potential are. On top of all that, all CDPR needs to do at that point is patch it and your $7mil invest came to nothing. I guarantee there are a thousand more effective exploits on the DARK WEB that can be had for free that could target way more machines with less risk.
It all smells like bullshit to me.
Thinking a little more..this is a really bad and dumb ransomeware attack.
Ransomware attacks are different from information theft. Different motive, different approaches, and definitely different approaches to publicity.
Ransomware is about leverage. The goal is to have the target WANT to pay you. Getting paid is the win. Carrying out your threat (whatever it is) is the loss state.
Good ransomware target has money to spend, isn’t set up for a quick recovery, and has an urgent and costly need to be in a working state. It’s why hospitals (for example) are such a tempting target. Not great at IT, and a “people will die!” motivation.
They chose the target poorly. CDPR may have money. But they have backups – the ransomware didn’t cost them much productivity. And they hit AFTER the game launched, when they weren’t under specific deadline pressure, so a few hours of downtime wasn’t worth a ton of money to them.
Also, why threaten to sell the code? Again, the goal is leverage. CDPR knows their competitors aren’t dumb enough to buy code that’s widely known to be stolen. Why not threaten to post the code online, creating a massive threat for hackers and allowing everyone in the industry to see their tricks? Your goal is LEVERAGE and the threat to sell hot code that doesn’t have a clear buyer isn’t the best leverage you have.
If the goal was to steal the code and threaten to sell it, there was no need for the ransomware. In fact, it’s counterproductive. The ransomware attack is a news story. It massively reduces the value of your stolen property, because now people know it’s stolen.
If your goal was ransom, you’d be better off quietly posting an encrypted copy of the source somewhere, and quietly mailing a ransom demand and a copy of the key to management with a threat to sell it.
If your goal was just to steal it and sell it to the highest bidder, then again ransomware is an incompetent approach. Why even let the target know it’s gone? Let alone pop up a list of demands on every machine in the place, thus GUARANTEEING that the story will get out. Your stolen product is worth much more if nobody knows it’s been stolen.
Just an incompetent attack by an incompetent threat actor. I have no doubt the $7m is an ego salve.
This is all very astute. If I do turn this into a video, I’ll probably uh… “borrow” some of these points.
(If you don’t want me to, then pay me $7 million by the weekend.)
Aside from the obvious points about lax IP sectors (China, India, Russia, Africa and South America based markets exist and do not care about your copyright), did you consider that someone might want the source for altruistic purposes?
A lot of random nerds made cash on crypto, stonks and other shenanigans recently. Why couldn’t one of them dropped some cash on the source?
The greatest explosion of powerful mods for a game generally comes after a source release, leak or hack. Knowing how things work let’s you create tools and engine mods that are beyond anything you can do with a black box engine and swapping out assets.
Because anyone wanting the code “for altruistic purposes” wouldn’t have tried to destroy it with a ransomware attack.
Ransomware does not normally exfiltrate the pre-encrypted files – that’s hard and there’s no reason to, because all you want is to sell the unlock.
Stealing and attempting to sell the source code is a completely different crime committed simultaneously against the same codebase, and one done very stupidly in this case.
I think Alec w is referring to the potential buyers as altruistic, not the original attackers
Borrow away!
I hadn’t thought about it, but what you’ve said is so obvious (once pointed out) that I’m now wondering what the real reason was that badly executed extortion could cover for.
It looks to me like each step is designed to increase publicity; first announcing “They’ve been hacked!” Then “We’ll sell it if they don’t comply!” finishing with a Big (undisclosed) number for the headlines of “Hackers sell for $7 Million”. Showing up after the games release, right about the same time frame as the outrage is simmering down, dragging them back into the news when they’d most like to be forgotten for a bit…
On the other hand, it’d take a large amount of effort to pull this off just for scandal’s sake; probably a way to make a profit somewhere, just not in the big public ransom demands.
As others have pointed out, we don’t know the final dollar amount (assuming it was actually sold), but assuming it was sold, seems like the final price was between $1M and $7M, and I’d bet closer to $1M. CDPR has confirmed that they believe the source was stolen, and there have been independent investigators/journalists who have confirmed that the data appears to be legit (as-in actually stolen), so I’m willing believe that part of the story with high likelihood. As far as whether the source was actually stolen, I agree with many of the conclusions above that this could easily be a smokescreen to cover the ransomers failure to get CDPR to bite and pay. However, my hunch while reading Shamus’ post was that a state-actor (or something sufficiently close to that – in some countries lines blur) is a very reasonable guess for who purchased the source if it was in fact sold. I see others are thinking the same. I work in an industry where that is a major threat and taken very seriously, and while this has not yet been commonplace in the gaming industry (as far as the general public is aware), given all the money involved in gaming I think it’s naive to assume that won’t change. There are a number of reasons a state-actor would want to acquire the code, ranging from purely selfish to openly malicious. Note that Cyberpunk 2077’s latest patch fixed a major DLL security vulnerability that modders discovered – imagine what someone with source code access might find, and combine that with the near 5 million PC sales at launch, with over 13 million total sales as of January. That’s a lot of attack vectors!
On a less serious note (but I guess one that’s a bit macabre), I couldn’t help but think of the following analogy for section #1 of the article: if someone bought the source code intending to release a game, that would be similar to a serial killer who has killed thousands of people in his home and is now selling that house exclusively to forensics specialists, of which he knows several/many will sweep his house thoroughly. Did he really get every one of the many thousands of drops of blood cleaned? How about the millions of strands of hair that have been through the house and belong to known missing people, did a single one slip through? Short version: agreed, this would be utter inconceivable nonsense!
1. They asked CDPR to pay up. Refused.
2. Then they put it up for auction. Nobody bid anything beyond joke and curiosity amounts.
3. A mystery buyer showed up and paid them an outrageous number.
Yes, of course that’s exactly what happened. It’s clearly bullshit. Even if they managed to steal it (which I doubt, because it’s not public yet), then they couldn’t sell it.
These hackers really should have sat down with Cyberpunk 2077 before embarking on this journey. Not only could they assess the current street value of the Cyberpunk code, but they could also follow the narrative of The Heist. A priceless industrial secret doesn’t mean much when no one wants to expose themselves criminally for it. And the people most likely to have given you money for it are also the ones most motivated to collect your head.
It would almost make sense if CDPR, like Yorinobu Arasaka, encouraged this theft from the inside. Massive lawsuits and criminal charges against any developer stupid enough to bite down on the offer, bank on some public goodwill. If no one bites, you lose nothing.
While I do agree that just having someone’s source isn’t THAT valuable, I think your main assumption that buyer is a small studio is not really plausible. If it did happen (we’ll never know if it did), I’d assume that the ones who bought the source were someone like EA. 7 mil is pocket change for them, and I’m fairly sure they’re not above something like that. I’d assume that an executive did it and stored somewhere, to later at some point show it to a team of devs they trust not to rat them out. The goal would be to just see if they can get anything out of it. Maybe they’ll borrow the ideas from the system of flags used to control the story flow, or maybe the monster AI has some revolutionary idea. They don’t need to use it directly, they can just get inspiration from it.
Absolutely no way would someone like EA do that.
Getting involved in this transaction would be a massive risk. Not only would they be exposed to lawsuits for using stolen code that belongs to CDPR, they’d also be at risk of blackmail from the thieves for having bought. They’d also be at risk of that team of developers reporting them.
Besides, if EA felt like spending millions on an engine, they’d just… pay their own people to work on that Frostbite engine they own. Same result, no risk involved with crimes.
$7,000,000 isn’t “pocket change” to anyone. Yes, that’d represent a small portion of their overall gross earnings, but you better believe that the accountants will record where every dollar goes, and that their Board of Directors will care about several million dollars in expenses that could otherwise be delicious profits. A payment to ‘Noneofyourbusiness Inc.’ or ‘Not-Hackers Ltd.’ isn’t going to slide by unnoticed.
I believe that one of your three conjectures is correct. But just to follow the thought experiment I can think of 4 other reasons to buy/use stolen code:
1. Education. To teach programmers who don’t have access to the normal industry. Think somewhere backward like North Korea. Or an African warlord who wants what the west has but doesn’t really have a clue on how to make that happen. A kind of “rule from the top” authoritarian where the basic idea is steal underpants — ???? — profit.
2. Cybercrime. To dissect the code to learn malware attacks against that kind of AAA software, or against CDPR specifically. Think state spy agencies or Russian mafia. Both of which have past instances of industrial sabotage to give friendly industries a leg up.
3. Inside job for personal reasons. Someone who knows exactly who will take the brunt of this inside CDPR. And wants to wreck their hated rival’s career. The public embarrassment is the point, not the code at all. Think office politics or some disgruntled employee who saw an opportunity to embarrass.
4. Stock market manipulation. The goal could be to drive the company price down. Either to buy directly or force some other deal behind the scenes. The code itself is irrelevant. It could be internal too. Like using a lowered stock price to avoid paying key employees bonuses or buying up cheaper stock for greater control.
But yeah, the most likely thing going on here is just a combination of lies and stupidity.
I don’t think it was sold
1) they tried to blackmail CDPR and they didnt play ball
2) they put it up for auction
3) they drew too much attention and got scared
4) they said they got an offer and then quickly ran for the hills
I’m inclined to think this was the scenario too. Even the ransom note left by the hackers suggests to me that the hacker was likely on the younger side; it practically reeks of the bravado and posturing used by young people who leap in without looking and haven’t thought far enough ahead about what they’ll do if the other side doesn’t play ball. There are some pretty niche reasons why somebody might want the source code (Steve C above lists some possible reasons), but the odds of such a buyer (with that kind of cash on hand) existing are pretty damn low.
Who in their right mind would pay money for somebody else’s code?
If you know something about programming you know the following thing about other people’s code:
– it does not compile first try. It may not compile ever, unless you know the exact toolchain used and all dependencies. Which are usually undocumented.
– They might be “very good” programmers: https://m.youtube.com/watch?v=-AQfQFcXac8 (the video is hilarious and the channel is interesting)
– The code is probably not or poorly documented.
– You will not like their code style.
– Let’s face it, some people’s code is improved in readability after encryption!
Disclaimer: not saying I am a good programmer myself. Other people is generic here. People might feel the same about my code.
As my IS training keeps stressing to me (ad nauseum) there is a lot of money spent on espionage. I actually wonder what $7 mil cost compares to your average espionage operation? It’s kind of chump change compared to the sorts of bribes and honeypots they use in the examples they give in training.
Like yeah, if a gaming company bought the source code for that much they would be idiots. However, there is an extensive infrastructure in place for countries–particularly China, which according to the State Department hits the US up for something like $600 billion a year in cyber-espionage thefts/attacks–buying ill-gotten high-tech secrets from corporations. Those entities aren’t as discerning as Sneaky Studios would want to be, they kind of just grab up everything they can.
China doesn’t care about releasing Witchman Chronicles, they want to teach Chinese engineers how to make their own Witchman Chronicles with the same level as skill and art as the engineers at CDPR. $7 mil for the stolen source code is a long-term investment toward that goal, the type of investment that they’ve not been shy about shilling out money for in the past. Assuming the hackers aren’t just blowing smoke out their ass, that is.
Possible use, though still unlikely to be able to make anywhere near a ROI on even the lowball numbers, would be to release the games on less reputable markets, potentially with an additional money-making payload inserted. Not sure if witcher 3, Cyberpunk have been cracked/pirated yet: releasing early to that market with an inbuilt crypto miner might yield something, or just go classic counterfeiting & find places to sell it for a big/small enough discount that the customers don’t ask questions.
I wonder how feasible it might be to just resell the games as is; trying to release them openly is obviously a no-go, but based on a recent steam story (Dev decided their name was “Very Positive”, got kicked off after enough people noticed it) you can probably sell quite a few copies as long as you stay under the radar.
Lets say you have some time, resources available, plan on waiting for the fuss to die down anyway, as it’d make things harder. While you wait, you set up a small, anonymous as possible (First problem point, don’t know how untraceable you can make a “studio”) studio with a conveniently close name, “CDI Project Rad” and release the underwhelming WlTCHER III, a basic shovelware alchemy game. Even if it gets manual review, you can show that it’s an actual game that isn’t stolen, just happens to have a similar name; 1 & 2 were flash games. Suspicious, but chances are it won’t get noticed among the other asset flips listed every day. Once it’s past that stage, it gets an update to v2, which is actually just the Witcher3 code, with any phone-home functions pulled, if necessary. (Potential failure point 3, but who’s going to check on every patch to every game?) Now you just have to set up/find a suitably “No Questions Asked” Key Reseller, and offer Steam keys to “The WlTCHER III” for enough of a discount to get someone to bite, but not enough to be suspicious. Person redeems it, can play the game. Any irregularities with it not showing up as “In Library” when looking at the store version, or the community tabs being empty can be blamed on steam being weird, unless you want to admit that you totally got hoodwinked into buying a pirated copy for $40.
It’s an overly complex plan that can’t make money fast without being discovered, but you could probably get a few thousand before anyone spoke up, at which point you already have your money & can hopefully disappear.
I’m sure there’s other issues my non-hardened-hacker didn’t pick up, but I suspect that a more dedicated group could find other ways to just sell the games.
EDIT: Should have read all the comments first, ContribuTor stated the same thing but much more eloquently. I should get some sleep.
EDIT EDIT: Apparently the code for GWENT has been leaked publicly: https://www.vice.com/en/article/88a3qk/cd-projekt-red-uses-dmca-to-take-down-tweets-sharing-stolen-game-code
I deal with responses to security breaches in my day job, and my assumption is that the 7 million number is BS. Like you said, there are very few buyers who could make use of it.
I’m surprised they didn’t just negotiate with CDPR to see how much they could get threating to publish the source code. While there aren’t too many people who could turn a profit by buying the code, I do think the loss of any trade secrets from it getting dumped on the internet could hurt.
While leveraging a threat of public release does seem like a better idea, CDPR has very little incentive to pay. Unlike with a physical hostage, you can’t ever be sure you got every copy of the source code back. It would be more of an ongoing blackmail situation than a one-time payment, and blackmailing a software company for not releasing digital information doesn’t seem like a particularly winning strategy.
I could see some BitCoin early enthusiast trading a bunch of worthless cryptocurrency in order to read someone else’s code for fun.
Just tossing something out there, re: the conjecture that if the source was purchased for a seven-figure amount (or, really, any amount) the most likely buyer was the Chinese government. (You can say “a Chinese company,” but in China that’s a distinction without a difference.)
If the Chinese government were involved in this at all, it is just as likely–likelier, even–that they would be not the buyers but the original thieves, and the ransom demand was a red herring, a distraction. Because of course no one would seriously believe Chinese agents would steal code for ransom, that would be stupid, so obviously China couldn’t possibly be involved in the theft of the code.
And as ContribuTor so adroitly explained up above, the way this theft and ransom demand was executed is so stupid in so many ways that it does give me pause to consider the possibility of a violation of Hanlon’s Razor.
Given their capabilities, it seems odd to create a false motive when you could just go undetected; while we can’t know for sure, as far as I’m aware, the only reason anyone knew that the data had been taken was the hacker announcing it in a bid for ransom. If the intent of the attack was to acquire the actual data, there would be no reason to alert everyone (Thereby burning any leftover entry methods) in a bid for a trivial amount of ransom money. Surely it’s easier to not even be a suspect than to engineer a red-herring.
A lot of interesting ideas here, but I’ve got a very hard time buying the China angle. As Shamus said, Unreal is much, much cheaper. Why would you pay 7 million when you can pay 0? There are also tons of free assets out there. Are these 7 million of outdated tech and assets really worth that much?
No, I think the hackers are definitely bluffing.
What are the odds that someone with lots of money and interest in the matter bought it just out of curiosity? I wouldn’t put it past the likes of Notch or Randy Pitchford to do such a thing.
Oh, this sounds hilariously alike to an O. Henry story. I wonder whether CDPR told the hackers to pay THEM instead, so they could just let it slide. :)
Some more dumb conspiracy theories:
1. CDPR staged all the hacking just to get some good publicity.
2. CDPR staged the hacking in an attept to prove that their games are still WORTH something. “Hey, look, someone paid $7 million for Cyberpunk 2077 source code! Would they have done it if it’d been THAT bad?”
3. CDPR staged the hacking to cover up for source code loss that they had accidentally deleted.
4. CDPR staged the hacking to cover up the fact that they had themselves sold on Dark web (but for FAR less than $7 mil).
5. CDPR staged the hacking to cover up the fact there had never been any source code… Okay, maybe this one was a bit far-fetched. :)
Ha! That’s a great point! (And a great read.) :)
Why, thank you! :)
I’m thinking less O. Henry and more Cohen Brothers. The setup here is very similar to “Burn After Reading”: somebody gets access to highly classified information without any ability to assess it’s actual worth, then decides to bluster their way through a poorly planned blackmail scheme that rapidly falls apart.
I’d say they’re both essentially the same story, just with different outcomes. We’ll have to wait and see which ending fits CDPR’s story. :)
It was Shamus wasn’t it…. He’s been the hacker all along. Or the buyer, possibly both!
Pretty clever ruse you’ve setup here. Pretend to be a humble Mass Effect rantsman on the internet for years, then after the BIG SCORE write up an article about how ABSURD the very idea of it is!
And all the sheeple nod their sheepish, floofy, wooly heads and no one suspects a thing. Hah, classic redirection technique!
You probably thought you’d get away with it too…
Is Shamus even your real name or just more lies?!
Yeah, what if his names actually Seamus?!
Who wouldn’t want the Witcher’s Code? It means you never have to get involved in politics.
On a more serious note, I rather like your first suggestion that it was bought by a lunatic, and I’m wondering how large your house needs to be to use The Witcher’s code for wallpaper.
Depends how small you print the code, I’d think
I think it’s wrong to assume that whoever bought the package (if that happened at all) was aiming for the old Witcher code. If they stole their entire repository, then that would include unreleased and possibly unannounced stuff, and it’s much more likely than it is this type of content they were after. Stolen Cyberpunk code almost certainly includes assets, storylines and groundwork for the upcoming DLCs.
Similar for vulnerabilities: you don’t have to reverse-engineer the code to find an existing vulnerability. You just have to look for a pull request for one that hasn’t been released yet.
Still hardly worth $7M, though :D
Personally my first preference is the theory that no actual sale took place, though some of the theories such as state actors could hold.
Just to round out all the possibilities, what if the buyer were to use the equivalent of stolen/counterfeit currency. So that if the buyer were to try to launder it instead, depending on the circumstances they would be likely to get pennies on the dollar. To arbitrarily make up a number I’ll say $350,000. At that price some of the scenarios make more financial sense. The seller gets stuck with currency that’s worth a fraction of what they thought, but what are they going to do, complain to the police?
Why assume the goal is to make money by selling software? With the source code, you could make a high quality nokey/cracked version to post on a torrent pretty easily. Once you’ve got people downloading THAT, you have your choice of revenue streams…
1- Your version is secretly its OWN ransom-ware attack with a well hidden timer. Six months from now, anyone who installed it better pay up…
2- Bot nets are still valuable. I don’t know if they’re 7 million valuable, but anyone downloading the Witcher 3 or Cyberpunk probably has a decent graphics card for cryptomining…
3- Can your pirated version claim to be so awesome that it can be connected to GOG Galaxy, the Epic Store, or Steam for achievements? Congratulations, you just stole someone’s login key. Have fun with their account…
If there was a seven-figure market for source code, there would be many, many more inside jobs. Security is good, but there are just too many people who necessarily have both a dangerous amount of access and the exact skills required to exploit it. I’m not saying it would be easy, or even successful– but with millions of dollars on offer, there would at least be more attempts.
There are numerous documented cases of espionage of national security-level material, where the thieves faced much greater risk for a much smaller pay-out, against targets that (hopefully) had much stricter security protocols. Even if we assume CDPR/EA/Activision are all locked down tighter than Los Alamos, PEOPLE WOULD TRY. The fact that by and large they don’t (except for a few specific spite-fueled incidents) tells me that there isn’t any significant incentive (except for spite).
“Is Brandan planning to spend additional time and money doing a drastic overhaul to the rendering code, or is he planning to release a game in 2025 with graphics that are a decade out-of-date?”
The Elder Scrolls 6, anyone? Nevermind the 20 year old engine, but I bet the graphics will be 5-10 years out of date.